×
Cyber Awareness Month is Here – Discover our latest MSP Partner Case Study
Read Now!Imagine a world where autonomous vehicles like Tesla drive us seamlessly through busy streets. Now, picture a scenario where hidden within this sophisticated technology lies a vulnerability, unknown even to the car manufacturer. This is not a scene from a sci-fi movie but a real event that unfolded when researchers at Technische Universität Berlin uncovered […]
Author
Date
Category
All Categories
Contents
Popular Posts
Product
Imagine a world where autonomous vehicles like Tesla drive us seamlessly through busy streets. Now, picture a scenario where hidden within this sophisticated technology lies a vulnerability, unknown even to the car manufacturer. This is not a scene from a sci-fi movie but a real event that unfolded when researchers at Technische Universität Berlin uncovered a hidden ‘Elon Mode’ in Tesla’s Autopilot system. This revelation not only raised eyebrows in the automotive industry but also rang alarm bells in the cybersecurity realm, highlighting how integral robust cyber defense mechanisms are in our increasingly digitized world.
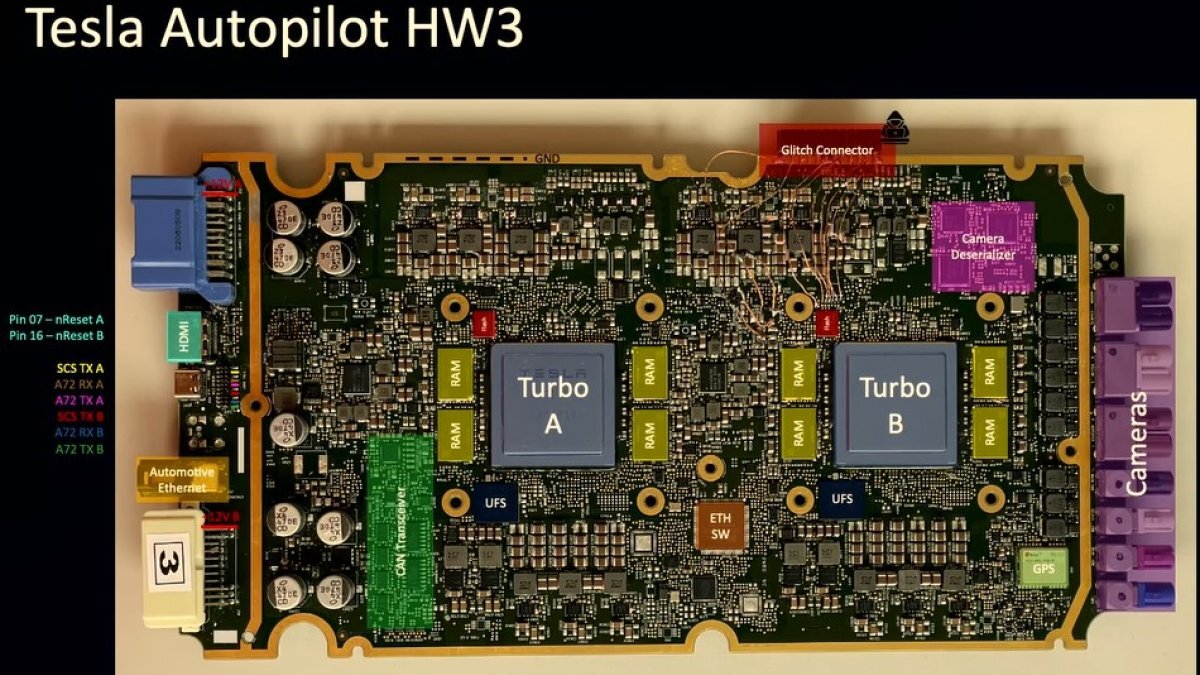
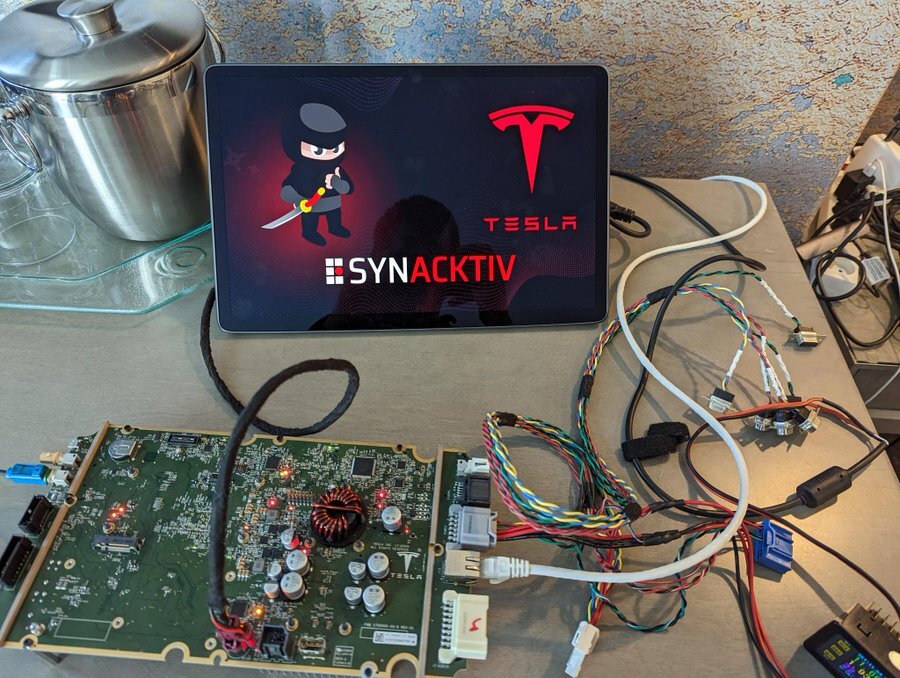
Three doctoral students from TU Berlin, with a mere €600 in tools, cracked open Tesla’s advanced technology. They bypassed the ARM64-based circuit board to reveal ‘Elon Mode’ – an autonomous driving feature operating without any driver input. This discovery, which Tesla had never disclosed, opens a Pandora’s box of questions about the safety protocols and security measures of autonomous vehicles.
The hack went beyond just exposing ‘Elon Mode’. It laid bare the underbelly of Tesla’s cybersecurity infrastructure, allowing access to sensitive data like cryptographic keys and GPS history. The simplicity with which this hack was executed is a stark reminder that no system, no matter how advanced, is immune to cyberthreats. The ease with which the students accessed Tesla’s systems is alarming, indicating potential gaps in the vehicle’s cybersecurity architecture. Such vulnerabilities, if exploited by malicious actors, could lead to dire consequences, ranging from data theft to unauthorized control of vehicle functions. The Importance of Robust Cybersecurity Measures: In the digital age, where our dependence on technology spans from self-driving cars to cloud-based services, the potential impact of cyberthreats has magnified. This incident is a clarion call for businesses, governments, and individuals to prioritize cybersecurity, reinforcing the need for cutting-edge solutions to protect digital assets.
Zero Trust Network Security, where trust is never assumed and everyone and everything that wants access to resources and data are thoroughly verified, is a critical weapon in organizations’ arsenal in response to such vulnerabilities. Timus Networks stands as one of the guardians in the realm of cybersecurity, championing the Secure Access Service Edge (SASE) and Zero Trust Network Access (ZTNA) model. By creating a software-defined security perimeter for an organization’s critical resources, business SaaS apps, and data, with a moat around them, Timus Networks minimizes risks related to data breaches and ransomware. Using the Timus solution, employees get secure, seamless, and always-on connectivity irrespective of their device, OS, or location.
With employees working from anywhere, and data now spread across hybrid cloud environments, the security perimeter is no longer restricted to the office behind the firewall. Creating conditional access while having granular control and deep network visibility has become increasingly difficult. Timus Networks achieves this with a 100% cloud-based architecture that creates a moat between unauthorized access and company resources. The Timus dedicated private gateway, stood up in the cloud for each client, hosts an adaptive cloud firewall and a secure web gateway and only grants access to business resources after going through a thorough set of zero-trust contextual behavior policies, one of the richest in the industry.
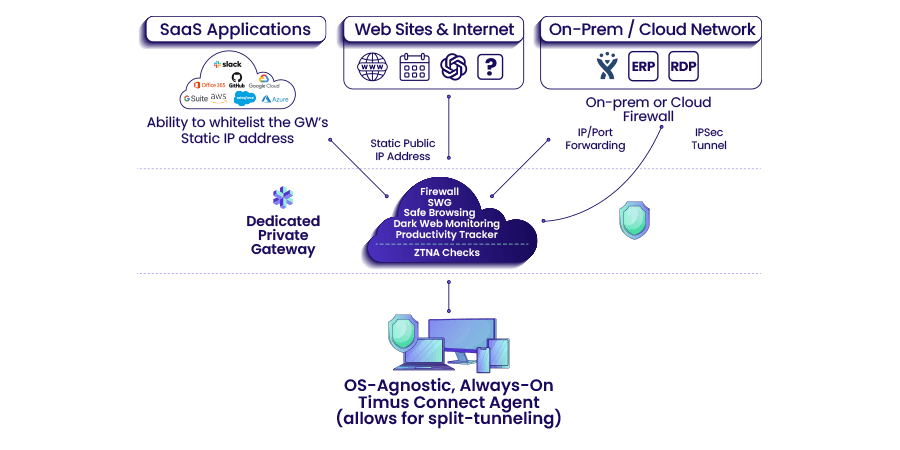
Timus Networks fortifies digital defenses with its dedicated cloud firewall and private traffic tunnels to on-premise firewalls, or cloud servers, enabling secure browsing and protected SaaS application access. Grounded in behavioral analytics, its conditional access policies ensure that only authenticated users gain network access, diminishing the risk of breaches.
The Adaptive Cloud Firewall by Timus Networks offers unmatched control and visibility over network traffic. Positioned as a single entry point to all resources, this firewall simplifies traffic and web filter rules, enhancing security and easing administration. Organizations can also get rich insights into their users’ and teams’ productivity at the application level utilizing the Timus Productivity Tracker feature built-into the solution.
With today’s distributed workforce, seamless and secure connectivity is non-negotiable. Timus Networks excels in providing always-on secure connectivity, supporting a wide range of devices and operating systems, ensuring comprehensive protection. The Timus solution makes VPNs obsolete with its super light-weight, always-on, and OS-agnostic agent across laptops, tablets, and mobile devices.
Timus Networks has been crafted with the needs of IT administrators in mind. Balancing ease of deployment with sophisticated security features, it offers a perfect blend for MSPs, backed by priority support and comprehensive onboarding.
In the face of sophisticated threats like the Tesla hack, Timus Networks’ solutions such as adaptive multi-factor authentication and micro-segmentation provide critical network access control, safeguarding against both external and internal threats.
Breaking the traditional confines of office-based security, Timus’s global points of presence ensure fast and secure remote connections. This worldwide reach is vital in a landscape where cyberthreats know no boundaries.
The Tesla hack is a valuable lesson in network security. Businesses must be proactive in identifying and mitigating vulnerabilities in their network infrastructure. Timus Networks offers a robust SASE solution that secures networks against a spectrum of cyberthreats, utilizing a Zero Trust approach to ensure that only verified and authorized users gain access to network resources.
As businesses navigate the complexities of the digital age, partnering with a cybersecurity expert like Timus Networks can provide peace of mind and a higher level of security. Timus Networks offers a solid SASE solution designed to protect against the ever-evolving landscape of cyber threats. From advanced firewall protection to sophisticated user authentication via ZTNA, Timus Networks equips businesses and their MSP partners with the tools they need to stay secure in an increasingly connected world.
The Tesla Autopilot hack serves as a wake-up call for businesses and individuals alike, highlighting the need for vigilant and proactive cybersecurity measures. In an era where digital threats can come from any direction, it’s essential to have a trusted partner like Timus Networks to navigate these challenges. With an R&D force that includes firewall experts with decades of cybersecurity and networking experience, Timus Networks is ideally positioned to help businesses fortify their defenses against the cybersecurity threats of today and tomorrow.
Ready to take your cybersecurity to the next level?
Discover how Timus Networks can safeguard your digital assets against vulnerabilities like those exposed in the Tesla Autopilot hack. Explore how we can help you protect your precious data on our website, or contact us to learn more about securing your network against the ever-evolving digital threats. With Timus Networks, you’re not just protecting data – you’re safeguarding your future.
Zero Trust. Adaptive Cloud Firewall. Secure Remote Access. In one.