Built for layered security, on the principles of Zero Trust Network Access. By providing a 100% cloud-based SASE solution, Timus fits seamlessly into existing infrastructure while protecting users at the edge. Deploy Timus SASE in less than 30 minutes to achieve secure, always-on connectivity.
Replace VPNs with Timus SASE
30-day free with a satisfaction guarantee
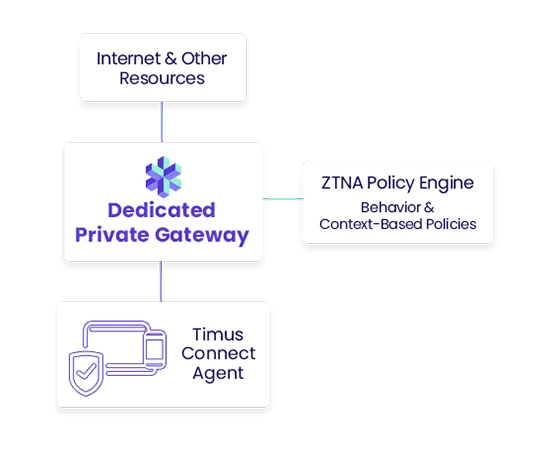
Zero Trust Network Access (ZTNA)
Everything Starts with Secure Access
Working from anywhere is only possible with secure remote access. Timus zero trust network access policy reduces risks by eliminating implicit trust and continually assessing users and devices. OS-agnostic agent.
Secure Web Gateway
Secure Your Business from Web Threats
Web based threats are eliminated by the Timus Secure Web Gateway before they arrive at your network. User access to unwanted or malicious web sites can easily be blocked. Customized category filtering allows easy compliance.
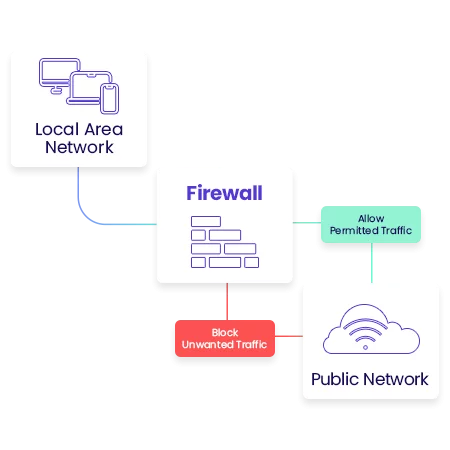
Adaptive Cloud Firewall
Adaptive Cloud Firewall with a Static IP Address
Manage access to web, cloud and internal applications without dealing with complex technical policies using the Timus L3-L7 Cloud Firewall. Control access to SaaS Apps by allow listing the Static IP of the dedicated GW. Unlimited IPsec tunnels.
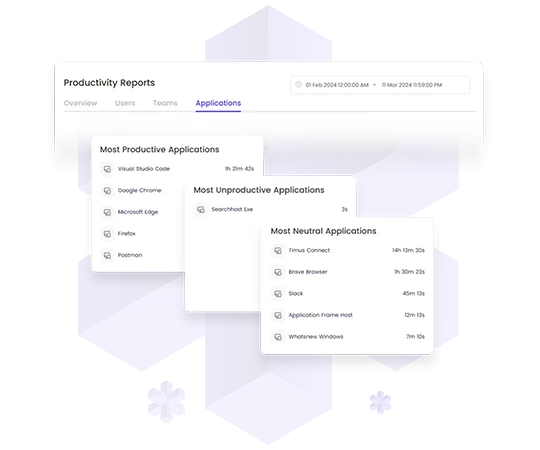
Productivity Tracker
Track Productivity Over Time
Timus SASE provides deep visibility into the network, allowing companies to track their employees’ and teams’ productivity over time.
Dashboards, logs and actionable insights with automated reporting. AI-driven segmentation of productivity.
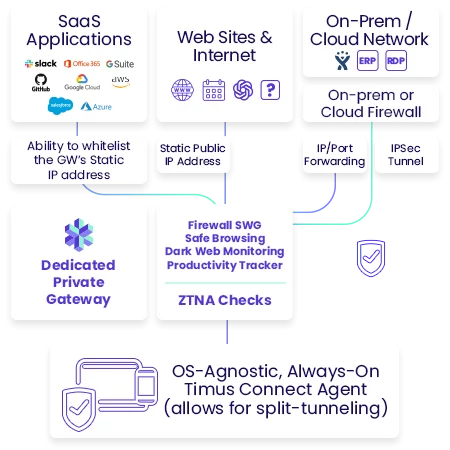
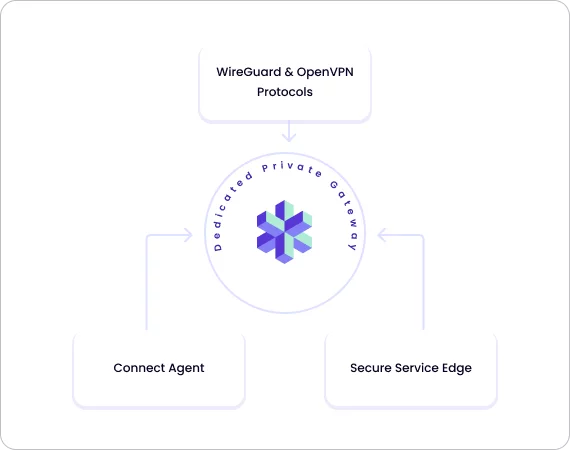
Secure Access Service Edge (SASE)
Deploy in 30 Minutes or Less
Timus dedicated private gateway sits between end users and all company resources, creating a software defined security perimeter based on identity. In addition to ZTNA, additional access control can be achieved by blocking all access to resources other than the allowlisted Static IP address.
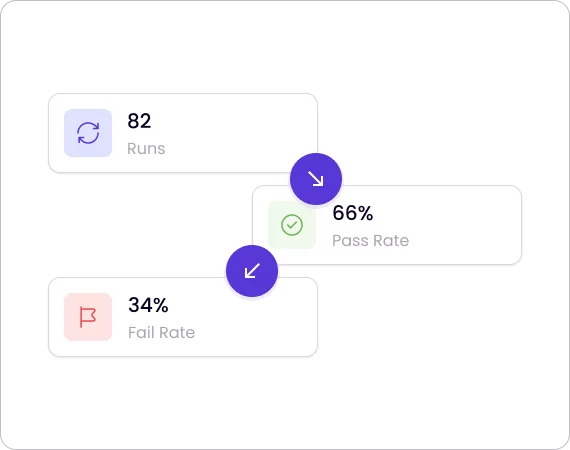
Device Posture Check
Unified Device Posture Management
Timus SASE DPC is integrated with several Endpoint Protection Platforms, such as Microsoft Defender, SentinelOne, BitDefender, and Heimdal Security. Integrations allow for combined endpoint and network security management, streamlining security workflows. Ability to isolate infected devices in real-time easily.
MSPs Are Moving to Modern Security. Are You?
Secure your clients, grow your revenue, and simplify your stack with Timus SASE.
30-day free with satisfaction guarantee
